Tutorials
Hands-on, step-by-step guides. Newest first.
This is the New Post
How am I pushing code from my PC to github
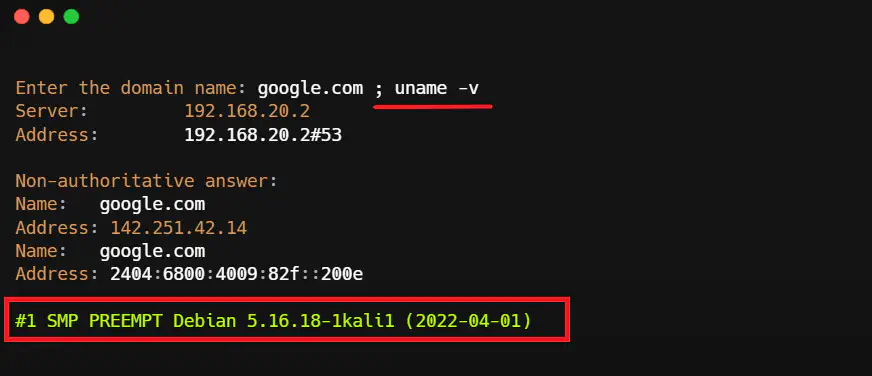
System Injection
How TLS works, what certificates do, and the configuration knobs that actually matter.
Maksud Site is new
How TLS works, what certificates do, and the configuration knobs that actually matter.

Building a Safe Malware Analysis Sandbox (Beginner-Friendly)
A defensive, ethical walkthrough for setting up a sandbox to analyze suspicious files safely

Intro to Web Security
A beginner-friendly map of the modern web threat landscape and the defenses that matter most.

Passwords vs Passkeys: What to Use in 2026
Understand the difference between passwords, password managers, and passkeys — and how to migrate safely.

Secure API Authentication Patterns
A practical guide to API keys, OAuth, JWTs, and service-to-service authentication — with common failure modes.

HTTPS & TLS Basics (Without the Math)
How TLS works, what certificates do, and the configuration knobs that actually matter.

Security Headers Checklist for Production
A practical, copy-paste friendly guide to CSP, HSTS, XFO, and other headers — with safe starting values.

SQL Injection Prevention: The Non-Negotiables
Parameterized queries, least privilege, and validation — the three pillars of SQLi defense.
